China’s Masked Drone Flights And The Quiet Rehearsal For Taiwan
A Chinese military drone has been flying over the South China Sea for months but not under its own name. By transmitting false aircraft identities mid-flight, Beijing may be testing more than surveillance endurance. It may be rehearsing confusion itself in a region already primed for confrontation.

Modern warfare rarely announces itself with sirens. Sometimes, it hums quietly above contested waters, transmitting a lie. Over the South China Sea, a large Chinese military drone has been flying regular missions for months. But it has not been flying under its own identity.
Instead, it has appeared – at different moments – as a sanctioned Belarusian cargo aircraft, a British fighter jet, even a civilian turboprop. On public flight-tracking platforms, it looked like something else entirely.
There were no dramatic interceptions. No emergency alerts. No official confrontation. Just coded signals (the kind that help civilian air traffic controllers and open-source analysts identify aircraft) quietly rewritten mid-flight.
In a region already thick with naval patrols, surveillance aircraft, submarines and rival territorial claims, that kind of digital masquerade is not a minor anomaly. It represents a shift. Not in hardware. But in intent.
The aircraft at the centre of these operations, flying under the call sign YILO4200, is widely assessed by open-source analysts to be a long-endurance Chinese military drone. Yet instead of transmitting its own registration data, it repeatedly broadcast the 24-bit digital identity codes of entirely different aircraft.
In an era where milliseconds can compress decision-making windows and escalation ladders are increasingly automated, identity itself becomes a tactical instrument. And that may be the most important signal of all.
What The Data Shows
Since August, at least 23 flights linked to the call sign YILO4200 have been logged over the South China Sea. The data, drawn from the civilian flight-tracking platform Flightradar24, shows a consistent pattern: departures from Hainan province, extended surveillance-style flight paths, and prolonged loitering over sensitive maritime corridors.
But the most striking element was not the routes. It was the identity.
The aircraft frequently appeared on public tracking systems as an Ilyushin-62 cargo aircraft operated by Rada Airlines of Belarus – a company sanctioned by the U.S. Treasury’s Office of Foreign Assets Control in 2024. At other times, the same signal broadcast identifiers associated with a Royal Air Force Typhoon fighter jet, a North Korean Il-62 passenger aircraft, and even an anonymous Gulfstream executive jet.
This was not random mislabeling. Nor was it a one-off data glitch.
In one instance spanning August 5–6, the aircraft reportedly switched digital identities mid-air – transmitting the code of an RAF Typhoon before cycling through three other aircraft identities within roughly 20 minutes, eventually “landing” under the Belarusian cargo aircraft registration.
In another case on November 18, the drone transmitted the identity of the Belarusian Il-62 while the actual aircraft was airborne elsewhere, flying a separate route near Belarus en route to Tehran.
The implications are significant. The 24-bit addresses that aircraft transmit are globally regulated and are meant to be unique digital identifiers. They are part of a system overseen by the International Civil Aviation Authority and are fundamental to how civilian aviation maintains situational awareness.
These transponder codes broadcast position, speed and direction. They form part of the automatic dependent surveillance–broadcast (ADS-B) system used by civilian trackers and some open-source intelligence communities.
While military-grade radar and encrypted defence networks are unlikely to rely solely on publicly available ADS-B signals, manipulating these identifiers can still introduce friction. Confusion. Noise.
The flight paths themselves reinforce the impression of deliberate surveillance rather than routine training. Many of the missions followed star-shaped or hourglass patterns – classic loitering profiles associated with intelligence-gathering drones.
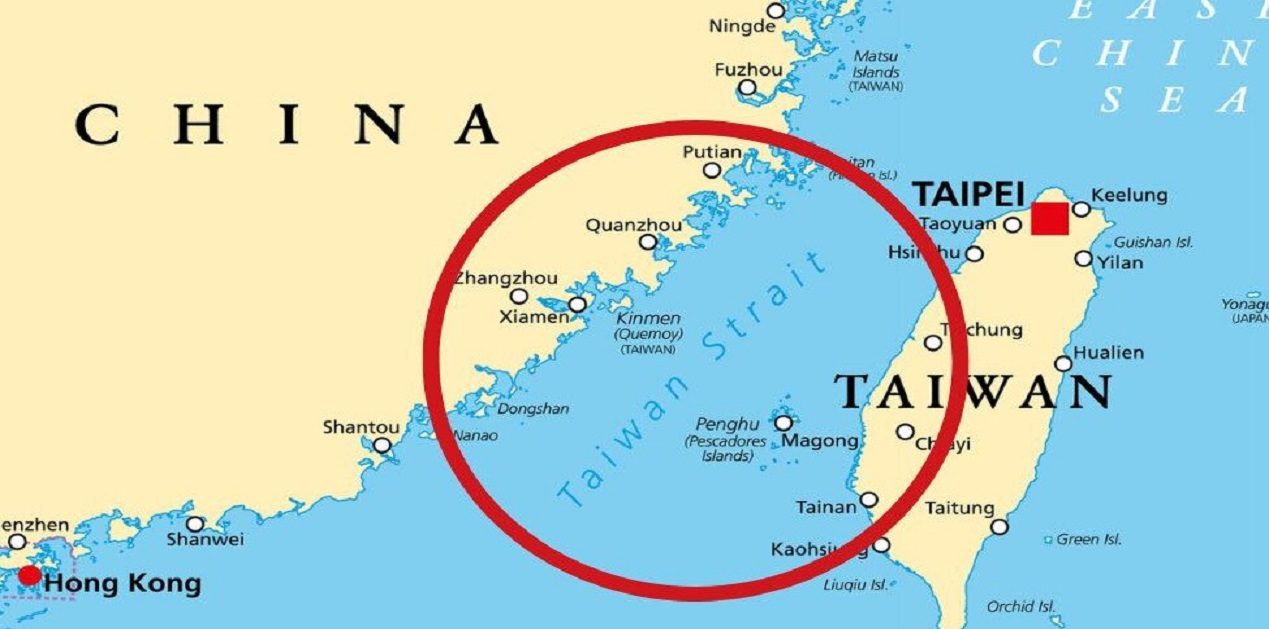
The routes extended eastward from Hainan toward the Philippines, near the disputed Paracel Islands, and down the Vietnamese coastline. Other trajectories pointed toward the Bashi Channel — the narrow choke point between Taiwan and the Philippines that provides China’s navy access to the wider Pacific.
These are not arbitrary corridors. They are among the most strategically sensitive waterways in the Indo-Pacific.
Hainan hosts major Chinese naval facilities, including submarine bases. The surrounding waters are dense with undersea activity. The Bashi Channel, meanwhile, is central to any future Chinese naval movement east of Taiwan.
When such areas are overflown repeatedly by an aircraft masking its identity, the act itself becomes part of the message.

Deliberate Deception, Not Technical Error
Could this have been accidental? Analysts who have examined the flight data do not believe so.
Aviation experts note that while miscodings and corrupted transponder data occasionally appear in civilian tracking systems, the pattern observed here differs in both scale and sophistication. Switching between multiple valid aircraft identities mid-flight is not typical of a random programming error.
Two pilots and several open-source intelligence analysts have indicated that transponders can, in theory, be recoded to transmit different 24-bit addresses. These digital identifiers are publicly documented. Reassignment, while unusual in civilian aviation, is technically feasible.
What makes the YILO4200 flights noteworthy is not merely that they transmitted incorrect codes but that they did so systematically, repeatedly, and in ways that coincided with real-world aircraft movements.
The fact that the genuine Belarusian Il-62 aircraft was airborne during at least one instance of identity masking eliminates the possibility that this was a clerical duplication or dormant registration reuse.
The behaviour appears intentional. More importantly, it appears experimental.
China’s military has increasingly expanded its grey-zone operations across the South China Sea and around Taiwan in recent years. Grey-zone tactics operate below the threshold of open conflict — using coast guard vessels instead of warships, militia boats instead of naval destroyers, cyber tools instead of missiles.
Digital deception fits comfortably within that toolkit.
Masking a drone as a foreign military jet or a sanctioned cargo aircraft could serve multiple purposes. It could test how quickly rival intelligence systems identify inconsistencies. It could create temporary ambiguity during moments of heightened tension. It could generate misleading data trails for open-source observers. Or it could simply condition the region’s monitoring systems to absorb a higher baseline level of informational distortion.
Military deception is as old as warfare itself. But in an environment increasingly defined by automated threat detection and compressed decision cycles, digital identity becomes a variable with operational value.
In highly networked conflict scenarios, targeting chains – from detection to decision to engagement – are increasingly assisted by algorithms. Even marginal confusion can impose delays. Even brief ambiguity can complicate attribution.
And attribution is central to deterrence.
If an aircraft appears on civilian trackers as a Belarusian cargo plane rather than a Chinese military drone, open-source analysts may initially misclassify the flight. Media reporting may lag. Diplomatic channels may hesitate. The information environment becomes muddied.
Singapore-based security analyst Alexander Neill described such actions as part of a broader effort to “muddy the waters” in advance of potential confrontation.
That phrase captures the essence of modern grey-zone competition. The objective is rarely outright invisibility. It is friction.
China’s military typically flies many of its drones “dark,” transmitting no public identifiers at all. Choosing instead to transmit false ones represents a different strategic calculation. Not absence – but misdirection. The distinction matters – going dark conceals presence. Masking presence manipulates perception.
As tensions continue to simmer across the Taiwan Strait and the broader South China Sea, the line between surveillance, rehearsal and signalling becomes thinner. These flights, taken in isolation, do not constitute aggression. They do not violate airspace in the conventional sense.
But they do suggest something more subtle: rehearsal of confusion. And in modern conflict planning, confusion is not an accident. It is engineered.
Why The South China Sea Is The Ideal Laboratory
To understand why these masked drone flights matter, one must first understand where they are happening.
The South China Sea is not merely a body of water dotted with disputed reefs. It is one of the world’s most strategic maritime arteries – a corridor through which trillions of dollars in trade pass annually. It is also a dense operating environment for naval forces, submarines, coast guards, surveillance aircraft and intelligence platforms.
Hainan province, from where these flights originate, is particularly significant. The island hosts major People’s Liberation Army Navy facilities, including submarine bases that support China’s expanding undersea deterrent. The waters south of Hainan are routinely patrolled and monitored, not just by Chinese forces, but by regional actors and the United States.
When a long-endurance drone departs from Hainan and flies eastward, it is not traversing empty space. It is moving through layered zones of maritime and aerial sensitivity.
Many of the YILO4200 flight paths extended toward the disputed Paracel Islands — claimed by China, Vietnam and Taiwan — and along Vietnam’s coastline. Others moved toward the Bashi Channel, the narrow passage between Taiwan and the Philippines.
The Bashi Channel is more than a map feature. It is a choke point.
In any future contingency involving Taiwan, China’s navy would need to access the broader Pacific. The channel provides one of the most viable routes. It is also heavily monitored by regional militaries and allied intelligence assets.
Overlay the reported flight paths onto a map of Taiwan and the picture sharpens further. The trajectories, when extended, intersect multiple military points of interest — particularly around Taipei and along Taiwan’s southern coastline. Eastern approaches bring the aircraft near Japanese and U.S. facilities in Okinawa and along the Ryukyu island chain.
These are not speculative interpretations. They are geographic realities.
If a state wished to test surveillance endurance, signal masking, electronic interference or reaction timing, this region offers the ideal proving ground. It is crowded enough to generate data. Sensitive enough to matter. Contested enough to blur intent.
In geopolitical terms, the South China Sea functions as both frontline and rehearsal space – a domain where signalling, deterrence and experimentation coexist.
And experimentation appears to be precisely what is underway.
China’s Expanding Grey-Zone Playbook
The phrase “grey-zone tactics” has become common in Indo-Pacific security discussions, but its meaning is often diluted. At its core, grey-zone activity involves coercive or strategic action that remains below the threshold of declared war.
It is pressure without open aggression. Presence without invasion. Escalation without explosion.
Over the past decade, China has refined this approach across maritime, cyber and air domains. Coast guard vessels swarm disputed reefs. Maritime militia fleets accompany naval patrols. Cyber intrusions target infrastructure without crossing into overt sabotage. Military aircraft conduct record numbers of incursions into Taiwan’s air defence identification zone — stopping short of violating sovereign airspace.
The masked drone flights fit into this continuum.
What distinguishes this episode is the integration of digital deception into physical movement. This is not simply a drone flying near contested waters. It is a drone manipulating the informational environment while doing so.
In modern military ecosystems, information flows are as critical as hardware deployments. Early warning systems, open-source intelligence communities, media monitoring networks and automated alert platforms all rely, to varying degrees, on transponder signals and aircraft identification codes.
Military-grade radar systems and encrypted tracking networks are far more sophisticated than civilian ADS-B data. Yet even highly advanced defence structures coexist within broader information environments. Public trackers influence media narratives. Media narratives influence diplomatic postures. Diplomatic posture shapes deterrence calculations.
By transmitting false 24-bit addresses – including those linked to foreign military aircraft – the operator is not necessarily attempting to blind advanced radar. Instead, it may be testing response layers.
- How quickly is the discrepancy identified?
- Which monitoring platforms flag it?
- Do public reports amplify it?
- Do foreign ministries seek clarification?
In tightly compressed escalation chains, even minor informational friction can have outsized consequences. Modern conflict is increasingly described as “kill chain” dependent – a sequence from detection to identification to decision to engagement. Analysts often emphasise that milliseconds can matter.
If digital masking introduces hesitation at the identification stage, even briefly, it becomes tactically meaningful.
There is also a psychological dimension.
Masking as a sanctioned Belarusian cargo aircraft, for instance, injects ambiguity. It forces observers to consider whether the anomaly is linked to sanctions evasion, intelligence transfer or unrelated civil aviation error. Masking as a British Typhoon introduces a different layer – one involving NATO-aligned forces. Each false identity shapes interpretation differently.
This is informational jamming without emitting a traditional electronic warfare pulse.
Rather than blocking signals, it alters them.
China’s military often flies certain platforms “dark,” transmitting no public identifiers at all. That approach conceals presence. But concealment has limits — it signals secrecy.
Deliberate misidentification, by contrast, manipulates perception. It plays within the system rather than outside it.
That distinction suggests strategic maturity in grey-zone doctrine: not just denying visibility, but shaping what is seen.

A Quiet Rehearsal For A Taiwan Scenario?
The most consequential question is whether these flights represent something more than regional signalling.
Several analysts have suggested that the patterns resemble rehearsals — not exercises in the traditional sense of visible drills with declared objectives, but rehearsals in informational preparation.
In a Taiwan contingency, the opening hours would be decisive. Rapid strikes, cyber disruptions, electronic warfare and maritime blockades would likely unfold in compressed timeframes. The informational environment would be saturated with claims, counterclaims and sensor data.
Confusion would not be incidental. It would be weaponised.
If a long-endurance drone can convincingly transmit the identity of a foreign aircraft, even temporarily, that capability could be integrated into a broader operational plan. It could obscure reconnaissance activity. It could complicate attribution. It could introduce ambiguity during the earliest detection phase of a crisis.
Consider the geography again. Flight paths intersect corridors that would be relevant in a Taiwan scenario — particularly the eastern approaches and the Bashi Channel. They traverse maritime zones where submarines operate and where allied surveillance assets maintain watch.
Overlaying those trajectories onto Taiwan’s map reveals repeated passes near military concentrations, especially around Taipei and along the southern coastline. Eastern arcs extend toward areas where U.S. and Japanese forces are stationed.
If these patterns were accidental, they would be remarkably consistent accidents.
The notion of rehearsal does not necessarily imply imminent conflict. Military organisations routinely test systems, probe responses and refine tactics over extended timelines. Preparation does not equal intention.
Yet preparation reveals priority.
Over the past several years, Beijing has repeatedly emphasised military readiness regarding Taiwan. The People’s Liberation Army has increased air sorties, naval manoeuvres and joint force drills. These visible exercises are often accompanied by less visible experimentation in cyber, electronic and information domains.
The masked drone flights align with this broader trajectory.
They suggest that preparation for a Taiwan contingency may not be limited to missile ranges and amphibious capabilities. It may also include rehearsing the fog of war itself.
In highly automated conflict environments, perception shapes action. Algorithms filter sensor inputs. Command centres triage alerts. Decision-makers operate under compressed timelines.
If those inputs are manipulated — even slightly — the tempo of response shifts.
Singapore-based analyst Alexander Neill described such activities as efforts to “muddy the waters” before confrontation. That phrase captures the strategic logic. In maritime conflict, water is rarely clear. Visibility is partial. Information is layered.
Adding digital misdirection into that environment deepens the opacity.
Taiwan may not be under imminent threat. There is no public evidence that these drone flights are linked to an immediate operational plan. But they do suggest conditioning — a slow adjustment of the battlespace’s informational texture.
In that sense, the rehearsal may not be for invasion alone. It may be for confusion.
And in contemporary geopolitics, confusion can be as decisive as force.
What This Means For The United States And Its Allies
For Washington and its Indo-Pacific partners, the most important question is not whether the masked drone flights can fool advanced military radar. It is whether they can complicate the broader response ecosystem that surrounds any crisis.
The United States maintains extensive surveillance coverage across the Western Pacific. Japan operates layered air and maritime monitoring systems, particularly around Okinawa and the Ryukyu island chain. The Philippines and Vietnam track activity in contested waters. Taiwan’s own defence infrastructure is permanently alert to aerial incursions and maritime movements.
In such an environment, no single signal determines action. What matters is fusion — the aggregation of radar inputs, satellite imagery, signals intelligence, open-source feeds and diplomatic reporting.
By manipulating publicly visible aircraft identities, the operator may not be seeking to blind sophisticated radar arrays. Instead, the objective could be to stress-test the connective tissue between systems.
- How quickly do discrepancies get reconciled between civilian tracking platforms and classified sensors?
- How do open-source analysts interpret anomalies?
- Does misinformation travel faster than correction?
In a crisis, these questions move from academic to operational.
The United States Indo-Pacific Command has repeatedly described Chinese military drills as rehearsals for potential confrontation scenarios. Rehearsal, however, is not confined to amphibious landings or missile launches. It includes informational preparation — understanding how adversaries observe, report and react.
There is also a signalling dimension directed outward. By demonstrating the ability to manipulate aircraft identity codes in a heavily monitored theatre, China signals that the informational battlespace is contested territory.
Allied militaries now operate in an era where the first hours of a conflict may unfold across digital dashboards before physical engagement becomes visible. False positives, misidentifications and signal distortions could generate hesitation or miscalculation.
That hesitation can cut both ways.
Deliberate ambiguity might slow an adversary’s response. But it also risks unintended escalation if misinterpretation cascades.
The South China Sea and the Taiwan Strait are already environments of compressed decision-making. Introducing systematic identity masking adds another layer to that compression.
For U.S. and allied planners, the takeaway may not be alarm but recalibration: assume that the informational layer of the battlespace will be contested from the outset.

When War Begins In Code
There was a time when deception meant inflatable tanks, false radio chatter or camouflage nets. Today, deception can be embedded in code.
The modern battlespace is algorithmic. Sensors feed automated classification systems. Artificial intelligence tools assist in anomaly detection. Targeting chains are increasingly networked and time-sensitive.
In such an ecosystem, data integrity becomes strategic capital.
Aircraft transponders were designed for safety and coordination in civil aviation. They were not intended as instruments of geopolitical signalling. Yet as civilian and military domains overlap — particularly in contested maritime zones — these systems become part of the wider strategic environment.
By recoding 24-bit addresses, an operator exploits the openness of civil aviation architecture. The manipulation does not need to be perfect. It only needs to create momentary uncertainty.
Momentary uncertainty is the modern fog of war.
Unlike traditional fog — caused by incomplete information — this fog is manufactured. It is introduced deliberately into a system that prizes speed and automation.
The difference matters.
When detection and engagement timelines are measured in seconds, the quality of data becomes critical. If an aircraft appears as a civilian platform rather than a military asset, initial classification may shift. If it appears as a foreign military aircraft, diplomatic sensitivities enter the frame.
Each variation influences interpretation.
This does not mean that advanced militaries will be deceived in any sustained sense. Classified systems are robust, multi-layered and designed to cross-check inputs. But even robust systems must operate within broader information ecosystems that include media, public trackers and diplomatic channels.
The informational domain is no longer peripheral to warfare. It is foundational.
And unlike missiles or warships, informational capabilities can be exercised continuously without crossing legal red lines.
That is the essence of grey-zone strategy in the digital age: persistent shaping rather than episodic confrontation.
In this context, the masked drone flights represent something more subtle than technological experimentation. They suggest rehearsal of perception management under contested conditions.
The Last Bit, The Signal Beneath The Signal
The flights linked to YILO4200 do not constitute an invasion plan. They do not confirm imminent military action. They do not prove operational timelines.
What they do suggest is preparation – methodical, incremental and layered.
—Preparation of geography through repeated patrols.
—Preparation of forces through visible exercises.
—Preparation of information systems through digital manipulation.
Taiwan remains the central strategic question in East Asia. Beijing views it as a core national objective. Washington views its stability as critical to regional balance. Allies calculate risks in real time. Each side calibrates deterrence carefully.
In such a climate, the most consequential developments may not be the loudest ones.

A drone flying under a false identity does not trigger headlines in the way missile launches do. Yet it speaks to a shift in how modern powers conceptualise competition.
The contest is no longer confined to territory or hardware. It extends to the reliability of the systems through which territory and hardware are observed.
If conflict were ever to erupt in the Taiwan Strait, the opening phase would likely be defined by speed, ambiguity and information saturation. The side that manages perception – that introduces friction into its adversary’s decision cycle – gains advantage.
The masked flights hint at conditioning for that possibility.
They reflect a strategic environment in which rehearsal occurs continuously, below the threshold of formal crisis. They illustrate how digital tools can be integrated into physical manoeuvres. And they ahow a broader reality: warfare in the 21st century begins long before the first kinetic exchange. Sometimes it begins with a signal. And sometimes, that signal is deliberately wrong.