Applications and types of cryptography in blockchain
Those, who are well aware of digital technology around themselves will know how blockchain has revolutionized the present age and why it is considered the future of trading and finance. On one hand, where blockchain supports decentralized currencies, on the other hand, blockchain can act as a potential platform for cloud storage facilities. By far, blockchain is considered the most secure cloud storage platform to date and is leading its way throughout the world. If you are considering to invest in Bitcoin, you can now easily trade Bitcoin with Fiat money.
Data storage, which is considered essential for the success of a process, is efficiently obeyed by blockchain technology, and that too in a cryptic way. Thus, no other than an authorized person can successfully access the data file and if accidentally it is accessed by some unauthorized entity, the data be cryptic, which will prevent undesired leaks. In this article, we are going to discuss the applications and types of the cryptography involved in blockchain practices.
What is Blockchain?
It is considered a peer-to-peer network wherein various peers or nodes that are in the form of computers are interconnected with the help of the network that is the internet. The word ‘blockchain’ is a mixture of two words that is ‘block’ means a record that involves the collection of data and other and other ‘chain’ is a database publicly accessed and stored as a list. The data and indexes are stored cryptically and this constitutes the most essential feature of blockchain. For some persons, blockchain being a unit of cryptography can be a confusing concept. For them, learning the basics of cryptography is the first-hand requirement.
Cryptography
The storage of information is most important as far as the prevention of data leaks is involved. For some projects, data storage is an important concern and some projects are so sensitive that they cannot afford data leaks. This is the time when blockchain comes to their rescue. Blockchain stores data in a cryptic manner and the role of third-party thus becomes nil. The storage, transfer, and access to the data are thus private and prevent unnecessary data engagements. The roots of the origin of word cryptography come from Kryptos and Graphein, which are Greek words that mean to keep hidden the entity and to write respectively. Along with cryptography, several terms associated with the parent term support the working of blockchain cryptically.
Types of cryptography
Blockchain cryptically performs different operations in three different ways that are cryptographic algorithms or asymmetric key cryptography. However, the main types were originally two types.
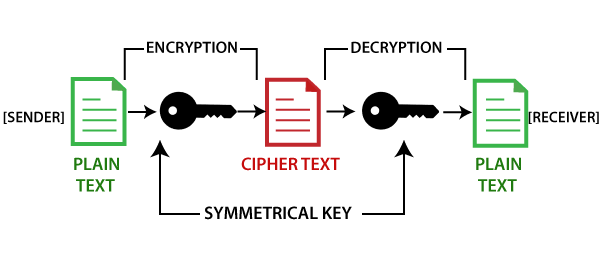
- Symmetric-key cryptography
Only one key is considered in this type of cryptography. The process of encryption and decryption is done by using only a single key. The major problem that arises while performing this operation is the problem of transferring the key between a sender and receiver. Leading to this is also called secret-key cryptography. Stream ciphers and block ciphers are the terms closely associated with symmetric-key cryptography.
- Asymmetric-key cryptography
Unlike symmetric-key cryptography wherein only one key is used, asymmetric-key cryptography uses two keys. The private and public, two different keys are used for the systemic process of encryption and decryption. The public key generated during the process is unique for safety purposes. Another anime for this type is public-key cryptography and is quite obvious due to previously discussed facts. When the ecosystem of data exchange is continuously expanding, this type of cryptography is generally adopted. Once the contact is successful, the purpose of the data interchange will be completed. If not, the process is either repeated or canceled as a whole.
Thus, the act of cryptography is not just technology but is an art that can be done only after learning the basics of it.




