
Several cyber attack can be launched via Dark Web. The most significant disadvantage of the Dark Web is its anonymity which raises the confidence level of the attacker and can quickly cyber attack the targeted victim.
CYBER ATTACK THROUGH DARKWEB

Correlation attacks
It is a full-fledged passive assault. The attacker controls the first and final routers in the TOR network and utilizes the timing and data properties to correlate the streams via those routers to undermine the anonymity of the TOR.
Previously, various government agencies could ruin the anonymity of many individuals by using correlation cyber attacks. Because it is a highly advanced mathematical procedure, there is no other way to block this assault. This type of attack is employed not just against software but also against users. Because it is a highly advanced mathematical procedure, there is no other way to block this assault. This type of cyber attack is employed not just against software but also against users.
For example, a dark-market admin may enter information about himself on the site, such as his age, prior criminal acts, and so on. It will assist the authorities in monitoring the Internet activity of all suspects and determining which one connects to the TOR network when the admin logs on. Carnegie Mellon University once carried out a correlation attack against a TOR network. The FBI paid $1 million for the information on the TOR users. Nonetheless, the correlation attack cannot be avoided. The attack harmed multiple websites, including Silk Road 2.0 and other child porn sites. To eliminate this form of assault, the only security mechanism available is the use of a reliable VPN.
Congestion attacks:
The congestion attack, also known as a clogging assault, watches the link between the two nodes and establishes a path between them. If the attacker blocks one of the nodes in the target path, the victim’s connection speed should vary. It is a full-fledged aggressive attack. Murdoch and Danezis disclosed a TOR assault in 2005 in which they used a clogging attack and timing analysis to identify all of the routers engaged in a TOR circuit. Congestion cyber attacks can also be used on routers with varying bandwidths. This attack is effective since the exit router is active, and we only need to discover a single node.
It also bypasses the conventional DoS constraint by utilizing the bandwidth multiplication approach, allowing low bandwidth connections to leverage high DoS bandwidth connections. This type of assault may be avoided by not using a predetermined route length. Second, end-to-end encryption is a possibility. Third, this type of attack may be avoided by disabling JavaScript in clients and causing connection delays.
Traffic and timing correlation attacks:
These are active end-to-end assaults. This is another type of de-anonymization assault. The entrance and exit relays are manipulated in this form of attack; by detecting the flow patterns in traffic traveling from entry relay to exit relay, the attacker may determine which server a client is speaking with. It is not essential to apply complicated mathematical procedures for de-anonymization.
When the number of clients utilizing TOR is small, traffic and timing assaults are simple. Otherwise, more sophisticated timing and traffic assaults are being used to de-anonymize the users. To avoid such assaults, TOR employs delayed, packet buffering, and shifting techniques.
For example, a Harvard University student was imprisoned for transmitting bogus bomb threats using TOR to avoid taking an exam. The emails were sent via Guerilla Mail, according to FBI data. Guerilla Mail is an email service that allows users to send out temporary emails. It embeds the sender’s IP address in all outgoing emails. According to the FBI, the student used TOR to send the emails. The FBI was able to identify the pupil thanks to correlation.
Traffic fingerprinting attacks:
It is a passive assault with a single end. It is a method of sniffing a website by studying the traffic flow pattern without removing encryption. In TOR, there are two ways to collect traffic statistics. In the first technique, the attacker intercepts Traffic at the entrance node. However, with this strategy, the victim does not need to connect to the attacker’s node. As a result, there is ambiguity. In a second way, the attacker will assume the role of a network operator, such as an Internet Service Provider (ISP), and will intercept Traffic between the victim and the TOR circuit’s entrance node.
It is a single-end passive attack. This is an effective method. Several defense mechanisms are available for this type of attack, namely HTTP with Obfuscation (HTTPS), pipeline randomization and Guard node adaptive padding and Traffic Morphing, etc. This is a powerful technique. Several security methods are available for this sort of attack, including HTTP with Obfuscation (HTTPS), pipeline randomization, Guard node adaptive padding, and Traffic Morphing.
Distributed Denial of Service (DDoS) attacks:
The attacker sends multiple fake requests to the target to slow down the connections or make them unavailable to the victim. It is not used to de-anonymize users. The sudden disappearance of Abraxas marketplace is one of the biggest mysteries. It’s unclear if the Abraxas marketplace was the victim of a DDoS assault or an exit fraud. Most accounts said it was an exit scam because the marketplace abruptly vanished as the bitcoin price skyrocketed. It is possible that the Abraxas marketplace was the target of a DDoS assault.
Users experienced very sluggish servers and trouble logging into the market before it was canceled. Secondly, on the Reddit Abraxas marketplace, admins state that they have suffered a major DDoS attack and will be back soon. Multi-variate threat detection can be used to efficiently detect DDoS attacks promptly.
Distributed Denial of Service (DDoS) attacks:
The attacker sends multiple fake requests to the target to slow down the connections or make them unavailable to the victim. It is not used to de-anonymize users. The sudden disappearance of Abraxas marketplace is one of the biggest mysteries. It’s unclear if the Abraxas marketplace was the victim of a DDoS assault or an exit fraud.
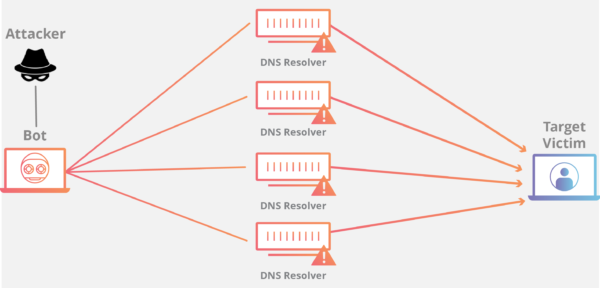
Most accounts said it was an exit scam because the marketplace abruptly vanished as the bitcoin price skyrocketed. It is possible that the Abraxas marketplace was the target of a DDoS assault. Users experienced very sluggish servers and trouble logging into the market before it was canceled. Secondly, on the Reddit Abraxas marketplace, admins state that they have suffered a major DDoS cyber attack and will be back soon.
Hidden services attacks:
Cyber Attacks against hidden services Access to resources can be gained without disclosing the user’s identity. The goal of the first node assault is to expose confidential services. The attacker’s relay attempts to become the network relay directly connected to the remote service server. This will instantly show the location of the concealed service. The attacker connects to the server through the infected node.
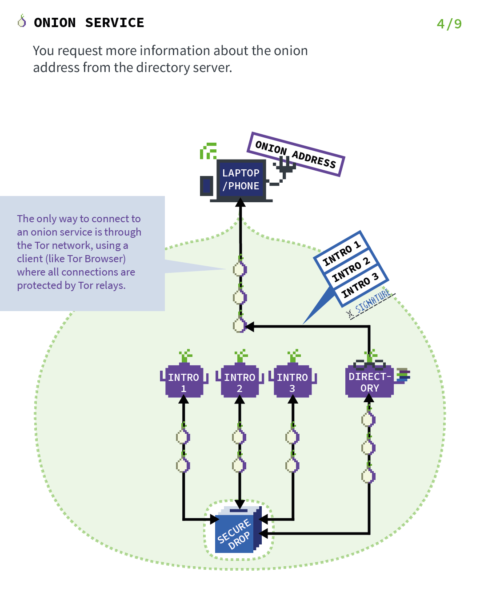
The malicious node assesses whether or not the given node is the first node by employing time analysis. Another attack, the Clock Skew attack, can select hidden services from a list of servers. The location of hidden services can be determined by comparing timestamps from several servers.
Phishing:
When an attacker wants to install malware or obtain sensitive information from the victim, he frequently employs phishing methods or appears to be someone else. In this type of assault, an attacker may send you an email that seems to be from a credible source. The email will either cut in on a link or attachment that allows you to install the virus. Three types of phishing have been described in the literature: spear phishing, whaling, and clone phishing.
Spear phishing is employed when a specific company is a target. This assault is used to target a massive number of people to obtain critical information. Whaling specifically targets senior or C-level executives in organizations. To deceive the victim, the attackers deploy targeted communications.
Clone Phishing involves presenting targets with a clone or replica of a contact they have already received. Because this cyber attack is predicated on a previously observed message, it is simple to target the user.
SQL injection (SQLI) attack:
Many servers store essential data by managing it with Structured Query Language (SQL). SQL injection attacks often target such servers. It can be dangerous if the database contains information on a customer’s bank account, credit card number, or other sensitive information. Unsanitized Input, Blind SQL Injection, and Out-of-Band Injection are the three forms of SQL injection cyber attacks that have been identified in the literature.
In Unsanitized Input, the attacker gives the user input that has not been appropriately sanitized or verified. Inferential SQL Injection is another name for blind SQL Injection. It does not immediately divulge data. The attacker scrutinizes the conduct. The disclosure of data is determined by the attacker’s needs. Out-of-Band Injection is a complicated procedure. It is employed when the attacker is unable to obtain the information through other means. The attacker produces the SQL statements, which, when executed, establish a connection with the external server. That external server is controlled by the attacker to obtain the needed data or information.
Credential reuse:
We’re all aware that we shouldn’t use the same login and password across the board. However, some users continue to engage in this activity. Once an attacker has a collection of Usernames and Passwords (which can be easily obtained from various black market websites), the attacker knows there is a probability they will be able to get in using the same login credentials. There are different password governors available, and they are instrumental in maintaining the many credentials you use.
Aside from these preventative steps, there is a variety of software and programs accessible to assist us in protecting ourselves from further damages and assaults on the Dark Web. They continuously monitor the activities and assist us in mitigating the adverse effects. This software includes DarkOwl Vision, Alert Logic Dark Web Scanning, ACID Cyber Intelligence, and Cybersprint for risk monitoring.
Limitations of the Existing Methods Against Cyber‑Attacks
According to the research of cybercriminal marketplaces, there has been a remarkable increase in the number of darknet listings that are potentially detrimental to the many dimensions. The literature has shown several shortcomings. Still, law enforcement needs a “heavy-handed” strategy to combat cybercrime by closing down websites. Approximately 70% of vendors do not communicate when it comes to purchasing malware over the Internet.
They utilize encrypted messaging apps like Telegram to keep talks out of the grasp of law authorities. There is no common malware or harmful actions pattern because they are tailored to the buyer’s goal and requirements. Dark Net merchants also provide a variety of methods for creating convincing lures for phishing campaigns by utilizing authentic paperwork and essential firm bills. These legitimate government documents and firm invoices may be purchased on the Dark Web.
Future Directions
There are several future directions in which organizations and users can work to protect themselves from such kinds of criminal activities over the Dark Web. For organizations, there is a need for a deep understanding of the threats posed by the Dark Web and those posed by custom remote access Trojans and malware mainly.
Organizations should utilize their ability to use the Dark Web for intelligence gathering by monitoring darknet marketplaces for the trade of company or customer data, malware, and for potential brand misuses, such as the sale of spoofed web pages and invoices, etc.
The literature has reported that companies are exploring the Dark Web for competitive intelligence gathering, recruitment, and secure communications. But still, there is a danger in exploiting those opportunities, including collaboration with criminals unwittingly by giving them access to their own networks.
Organizations must adopt layered defense mechanisms that utilize application isolation to identify threats and have in-depth threat telemetry to stop cybercriminals from getting into corporate networks.
edited and proofread by nikita sharma




