The Growing Menace of Cybercrime: Government blacklists 8 entities

The Growing Menace of Cybercrime: Government blacklists 8 entities
Delhi, New Delhi An official release states that as part of a major crackdown on SMS scammers, the government has blacklisted eight ‘key entities’ that are behind the SMS headers used to send over 10,000 fraudulent messages in the last three months. I went.
It stated that through the Sanchar Saathi initiative, the Department of Telecommunications (DoT) in partnership with the Ministry of Home Affairs (MHA) has taken decisive action to safeguard citizens from potential SM frauds.
Information regarding the exploitation of eight SMS headers to send phony messages and conduct cybercrimes was given by the Home Ministry’s Indian Cybercrime Coordination Center (I4C).

About 14(C) of the Indian Cybercrime Coordination Centre
The Ministry of Home Affairs, Government of India, launched the Indian Cybercrime Coordination Centre (I4C) as an effort to address cybercrime in the nation in a coordinated and thorough manner.
With a focus on improving citizen satisfaction, driving change in India’s overall capacity to combat cybercrime, and enhancing coordination between various law enforcement agencies and stakeholders, I4C aims to address every issue related to cybercrime for the benefit of its citizenry.
On October 5, 2018, the Indian Cybercrime Coordination Center scheme was approved. Since its launch, it has aimed to improve the country’s ability to combat cybercrimes as a whole and foster efficient cooperation between law enforcement agencies. The Honorable Home Minister dedicated the I4C to the Nation on January 10, 2020.
In the last three months, more than 10,000 fraudulent messages were sent with these eight headers, it was reported. These eight SMS headers belong to eight significant entities that have been blacklisted.”Along with their 1522 SMS content templates and 73 SMS headers, all 8 PEs have been placed on a blacklist.
Telecom operators can no longer use any of these main entities, SMS headers, or templates to send SMS messages. These organizations have been further prohibited by DoT, and citizens may experience harassment.
In the context of telecom, “Principal Entities” refers to the company or legal body that uses SMS to deliver commercial messages to telecom users. To send commercial communications, the ‘head entity’ is designated by an alphanumeric string called HEAD. By placing these organizations on a blacklist, DoT has avoided possible harassment of its citizens and reaffirmed its commitment to shielding them from online crime.
“Citizens can report suspected fraudulent communications on Chaksh Suvidha Sanchar Saathi to help the DoT in preventing misuse of telecom resources for cyber crimes and financial frauds,” the press release stated.
It issued a warning that using mobile numbers for telemarketing purposes is prohibited.
A customer’s connection will be cut off upon the first complaint if he uses his phone line to send promotional messages, and his name and address might be placed on a two-year blacklist.
Prefixes such as 180, 140, and others can be used to identify telemarketing calls. It is prohibited to use 10-digit phone numbers for telemarketing purposes. The release stated, “Use the DND (do not disturb) service or dial 1909 to report spam.”

What is Cyber Crime?
Any illegal activity involving a computer, network, or networked device is called cybercrime.
While the majority of cybercriminals commit crimes to make money, some of them target computers or other devices specifically to harm or disable them. Others disseminate malware, illicit information, photographs, and other materials via computers or networks. Certain cybercrimes combine the two tactics of targeting computers and infecting them with a virus that spreads to other devices and occasionally even entire networks.
Money is one of the main effects of cybercrime. Cybercrime encompasses various financially motivated illegal activities, such as ransomware attacks, identity theft, email, and internet fraud, and attempts to steal credit cards, bank accounts, or other payment card information.
Backup data should be protected even more so because hackers may target personal or company information for theft and resale.
The following three categories describe how the U.S. Department of Justice (DOJ) classifies cybercrime:
- Crimes where the goal is to obtain access to a computer device, such as gaining network access.
- Crimes involving the use of computers as weapons, such as launching denial-of-service (DoS) attacks.
- Crimes in which a computer is used as a tool for the commission of another crime, such as storing data that was obtained illegally on a computer.

The United States is a signatory to the Council of Europe Convention on Cybercrime, which defines cybercrime as a broad range of malicious activities, such as unauthorized data interception, system interferences that jeopardize network integrity, availability violations, and copyright infringements.
The requirement for internet connectivity has made it possible for cybercriminals to commit crimes more frequently and at a faster rate because they are no longer required to be physically present. Computer-based versions of financial crimes, including ransomware, fraud, and money laundering, as well as crimes like stalking and bullying, are made easier to commit by the internet’s speed, convenience, anonymity, and borderlessness.
Cybercriminal activity can be carried out by individuals or groups with relatively little technical skill or by highly organized global criminal groups that could include skilled developers and others with relevant expertise. To further reduce the chances of detection and prosecution, cybercriminals often choose to operate in countries with weak or nonexistent cybercrime laws.
Cybercrime can be committed by highly organized international criminal groups, which may include competent developers and other experts in the field, or by individuals or groups with relatively low technical skills. Cybercriminals frequently opt to operate in nations with lax or nonexistent cybercrime laws to further decrease the likelihood of being discovered and prosecuted.
How does cybercrime work?
Attacks by cybercriminals can start anywhere there is digital data, a motive, and an opportunity. Cybercriminals range from lone individuals who engage in cyberbullying to actors with state sponsorship, like China’s intelligence services.
Cybercrimes are, for the most part, naturally distributed; they rarely happen in a vacuum. That is, to carry out their crimes, cybercriminals usually rely on other players. This applies to malware developers who resell code on the dark web, illicit drug distributors who use cryptocurrency brokers to hold virtual currency in escrow, and state threat actors who pilfer intellectual property by using technology subcontractors.
Cybercriminals carry out cyberattacks using a variety of attack vectors, and they are always looking for new ways to accomplish their objectives without being discovered or apprehended.
Although malware and other software are frequently used by cybercriminals, social engineering is typically a key element in the execution of the majority of cybercrimes. Phishing emails are a significant part of many forms of cybercrime, but they are particularly important for targeted attacks like business email compromise, where the attacker tries to look like a business owner via email to persuade staff to pay fake invoices.
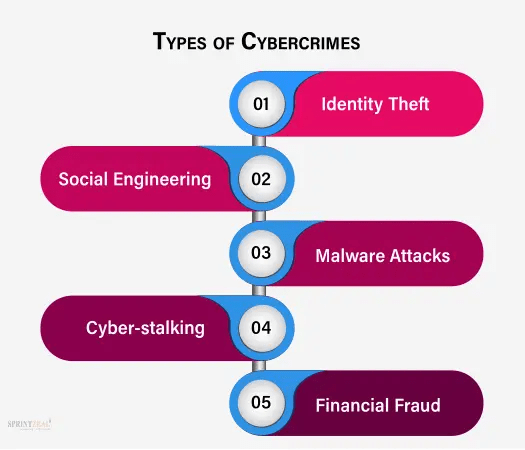
Cybercrime types
Cybercriminals can carry out malevolent attacks using a wide variety of cybercrime types. Though there are many different ways that cybercriminals get paid, most attackers do cybercrimes to make money. Particular categories of cybercrimes consist of the following:
Cyber-Abuse– This crime consists of an attack or threat of attack combined with a demand for cash to put an end to the aggression. A ransomware attack is one type of cyberextortion. Here, the attacker accesses the systems of the company and encrypts all documents and files that could be valuable, rendering the data unreadable until a ransom is paid. Payment is typically made with a cryptocurrency, like Bitcoin.
Hacking with cryptocurrency- Without the user’s permission, this attack mines cryptocurrencies inside browsers using scripts. Installing cryptocurrency mining software on the victim’s computer is one method of crypto-jacking attacks. A lot of attacks rely on JavaScript code that, if the user’s browser has a tab or window open on the malicious site, performs in-browser mining. Since the in-browser mining code is executed when the affected page is loaded, no malware needs to be installed.
Theft of identity– This kind of attack takes place when someone gains access to a computer to steal a user’s data. The data is then used to either steal the user’s identity or gain access to their credit card and bank accounts, among other valuable accounts. On darknet markets, identity information is bought and sold by cybercriminals who also offer financial accounts, webmail, streaming video and audio, online auctions, and other account types. Identity thieves also frequently target personal health information.
The fraud of credit cards– This type of attack takes place when malevolent hackers breach the systems of retailers in an attempt to obtain the credit card or banking information of their patrons. On darknet markets, where hacking groups that have taken large amounts of credit cards make money by selling to more junior cybercriminals who make money by using credit card fraud against individual accounts, stolen payment cards can be purchased and sold in bulk.
Cyber-espionage- Cybercriminals commit this crime by breaking into networks or systems to obtain private data that is owned by the government or another entity. Attacks are driven by ideology or financial gain. In addition to using network-connected devices, like webcams or closed-circuit TV cameras, to spy on a targeted individual or group and monitor communications, including emails, text messages, and instant messages, cyberespionage activities also involve cyberattacks that collect, alter, or destroy data.
Software theft- Software that has been illegally copied, distributed, and used for either personal or commercial purposes is the target of this attack. Software piracy is frequently linked to patent infringement, trademark violations, and copyright violations.
Leave-taking fraud- The exit scam is a long-standing crime that has a digital variant thanks to the dark web. Currently, administrators of the dark web redirect virtual currency stored in escrow accounts for marketplaces to their accounts; in essence, they are thieves taking advantage of other thieves.
Common instances of online fraud
Distributed denial-of-service (DDoS) attacks are a frequent type of cybercrime attack that works by overloading a network’s communications protocol and forcing it to respond to connection requests. DDoS attacks can be used to divert attention away from another attack or exploit being carried out concurrently, although they are also occasionally conducted maliciously or as a component of a cyberextortion scheme.
Malware is a prevalent cybercrime that can harm software, systems, and data that is stored on them. Malware that encrypts data or locks down victim systems until a ransom is paid is known as ransomware.
Hackers can also take over websites to alter or remove content or gain unauthorized access to or alter databases. For instance, hackers can insert malicious code into a website using Structured Query Language injection exploits. This code can then be used to exploit database vulnerabilities on the website, giving a malevolent hacker the ability to access and alter records or obtain unauthorized access to sensitive data, including trade secrets, intellectual property, credit card numbers, and customer passwords.
The sale of illicit goods, such as guns, drugs, or counterfeit goods, as well as the creation, distribution, or solicitation of child pornography, are other frequent instances of cybercrime.
Cybercrime’s effects on businesses
It is challenging to determine the true cost of cybercrime with accuracy. According to Cybersecurity Ventures, cybercrime is predicted to increase by 15% yearly worldwide and reach $10.5 trillion by 2025.
Even though cybercrime can result in large financial losses, criminal cyberattacks can also have other disastrous effects on businesses, such as the following:
A company’s value may decline following a security breach due to harm to investor perception.
A cyberattack may result in higher borrowing costs for businesses and more challenges in raising additional capital.
Companies that have neglected to protect their customers’ data may face fines and penalties if sensitive customer data is lost. Businesses that have a data breach may also face legal action.
Customer confidence in a company and its ability to protect its financial data is eroded by damaged brand identity and reputation following a cyberattack. After a cyberattack, businesses risk losing their existing clientele as well as their ability to attract new ones.
Cybercrime’s effects on a country’s defense
Cybercrimes are a major priority for the DOJ because they can have an impact on national security and public health. The Department of Justice (DOJ) agency tasked with fighting cybercrime is the Federal Bureau of Investigation (FBI) Cyber Division. Increasing cyberspace’s security and resilience is a key homeland security goal, according to the Department of Homeland Security (DHS).
The goal of the DHS’s Cybersecurity and Infrastructure Security Agency (CISA) is to increase the physical and cyber infrastructure’s security and resilience. There are specialized divisions within other organizations, like the U.S. Immigration and Customs Enforcement (ICE) and the U.S. Secret Service (USSS), devoted to the fight against cybercrime.
For instance, the USSS’s Electronic Crimes Task Force looks into cases involving electronic crimes, especially assaults on the country’s vital and financial infrastructures. Additionally, USSS is in charge of the National Computer Forensics Institute, which offers computer forensics training to judges, prosecutors, and state and local law enforcement.
Online complaints from victims of online crimes or interested parties are accepted by the Internet Crime Complaint Center, a collaboration between the FBI, the National White Collar Crime Center, and the Bureau of Justice Assistance.
Ways to stop cybercrime
Businesses can lessen their vulnerability to cybercrime by implementing an efficient cybersecurity strategy that applies a defense-in-depth method to safeguarding systems, networks, and data, even though it is impossible to eradicate cybercrime and guarantee total internet security.
Companies can lower their risk of cybercrime by doing the following:
- Provide employees and the company with clear policies and procedures.
- Make plans for responding to cybersecurity incidents to support these guidelines.
- Describe the security precautions taken to safeguard company data and systems.
- Use physical security keys or apps that support multifactor authentication (MFA).
- When it’s feasible, turn on MFA for each internet account.
- Speak with a financial manager to confirm requests for money transfers verbally.
- Make rules for your intrusion detection system to identify emails with extensions resembling those of your business.
- Examine every email requesting the transfer of funds to see if there are any unusual requests.
- Employees should get training on cybersecurity policies, procedures, and what to do in the event of a breach.
- Keep all software releases, patches, and websites, endpoint devices, and systems up to date.
- To lessen the harm in the event of a ransomware attack or data breach, regularly backup your data and information.
By encrypting local hard drives and email servers, utilizing virtual private networks, and utilizing a private, secure domain name system server, one can further strengthen information security and resistance to cybercrime exploits.
With the increasing use of digital technologies, cybercrime is becoming a more serious threat. Safeguarding our digital world requires understanding the different types of cybercrime, realizing its impact, and putting strong counter measures in place.
Individuals, companies, and governments can collaborate to reduce risks and defend against the constantly changing cyber threat landscape by remaining watchful and proactive.




