
Android is the most prevailing smartphone operating system at the moment. On the other hand, users are concerned about the security of their personal information, given the fast-expanding amount of malware for Android, which much outnumbers that for different platforms. Antivirus software promises to successfully protect mobile devices from viruses, and many versions are accessible for free or at a low cost. Various reports confirm their effectiveness, with very high detection rates.
While more antivirus products for Android are appearing, and consumers are feeling the need to defend themselves against an increasing quantity of infections, the overall risk scenario on the Android platform remains opaque.
As a result of the malware threat level:
1) the overall risk condition for Android users
2) The amount of protection provided by Android antivirus software is opaque and difficult to judge.
A current assessment of the general Android malware risk situation focuses on the level of protection provided by existing antivirus software for Android. Using representations of known Android malware and Android exploits, we’ll run a series of tests on Android antivirus software.
Android Risk Assessment
Two types of reports have significantly affected the public’s impression of Android security: On the one hand, antivirus manufacturers often produce threat reports on the condition of malware threats for numerous platforms, including mobile platforms, because they have access to the most extensive set of malware samples. On the other hand, test reports of antivirus product tests are published by periodicals, companies, and institutes. Both studies contribute to the Android platform’s assessed risk rating. In this scenario, the risk is a function of both the threat and the level of protection.
Threat Reports
Threat reports are released regularly by several antivirus manufacturers. Most of the time, these contain details about specific malware samples, which are on the rise. Based on these unique malware sample statistics, many people conclude that the malware threat scenario on Android is rapidly worsening.

Any tiny modification in a malware sample, on the other hand, makes it “unique,” as its hash/checksum differs from that of all other instances in the same malware family. As a result, there could be dozens or hundreds of different samples with similar functionality. To get around multiple detection techniques, malware is frequently updated with minor alterations. To evade checksum-based detection, single bits and character strings can be modified, and executable obfuscation can be used to avoid signature- or heuristic-based detection, and so on.
The number of devices vulnerable to specific assaults or distribution channels, actual infection numbers, and new malware families is far more relevant for threat assessment. These are occasionally addressed, although they are rarely the focus of attention. In addition to danger reports, news releases frequently warn about growing hazards to Android users.
AV-Test [5] has conducted one of the most notable and comprehensive Android antivirus software testings to date. It uses the same approaches that are used in antivirus tests on other systems like Microsoft Windows. Most critically, here is a comparison of all products’ retrospective detection rates.
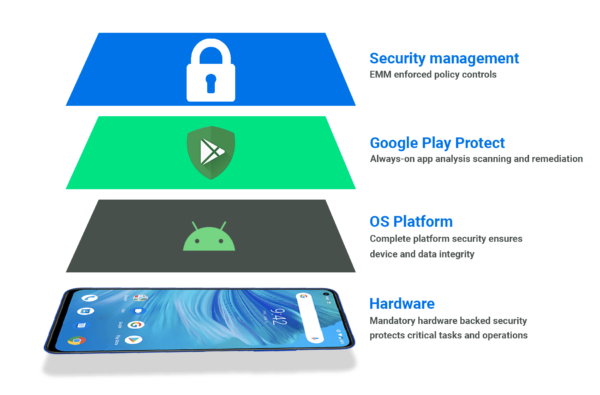
The Android platform has fundamentally different approaches for controlling software access to operating systems, devices, and other programs’ resources. On desktop policies, most software is a priori considered trusted and has, once installed, far-reaching access to the system’s, the users’, and other software’s data on that system.
AV-Test [5] has completed one of the most comprehensive and well-known Android antivirus software tests to date. It employs the same techniques as antivirus tests on other operating systems, such as Microsoft Windows. Most importantly, below is a comparison of the retrospective detection rates of all products.

While this approach, because it is retrospective, does not accurately depict the level of protection provided by each product at the time of the emergence of a new malware threat, there are additional issues on the Android platform that make these test methodologies less appropriate for evaluating the level of protection provided by the examined products.
As a result, antivirus software on Android cannot do full file system scans or filesystem monitoring. This has serious ramifications. Otherwise, innocent apps may begin downloading and running executables from their working directories – a behavior that Android does not control or restrict.
Android antivirus software is unable to detect this. As a result, retrospective detection rate assessments of Android antivirus cannot cover these assaults. Such attacks are viable and straightforward to carry out. On the other hand, antivirus tests reveal high detection rates, implying near-perfect protection of devices with 90% or more detection rates.
Antivirus Tests: Methodology
In the end, Android antivirus software must rely on two key sources of data to detect malware:
1. Package database3
2. Package files (APK files) of installed apps
Package names and file locations are stored in the package database. Because Android antivirus software can’t see what’s in the directory with installed packages, it has to rely on the package database to tell it where the containers are. Following that, these package files can be read and examined using standard antivirus detection procedures. On the Android platform, however, all files added after installation are invisible to antivirus software.
Distribution Channels
Any data transmission or communication route can be used to launch an attack or spread malware. Typical ways for assuming control of channels that aren’t meant for transmitting software can still be used to take control of tracks that aren’t meant for sharing software.
As a result of incorrect programming, you have control over the control flow of any app or service. USB, Bluetooth, and NFC connections, as well as barcodes, are among these vectors. Unsecured wireless connections that can be used to inject data, QR codes processing GSM/UMTS/LTE radio packages incorrectly, etc.
The official Google+ page is an excellent example of a communication channel that is built to convey software. App stores such as the Google Play Store and third-party app stores are available. The following are the most common infection routes for common malware discovered in the wild today:
App Markets
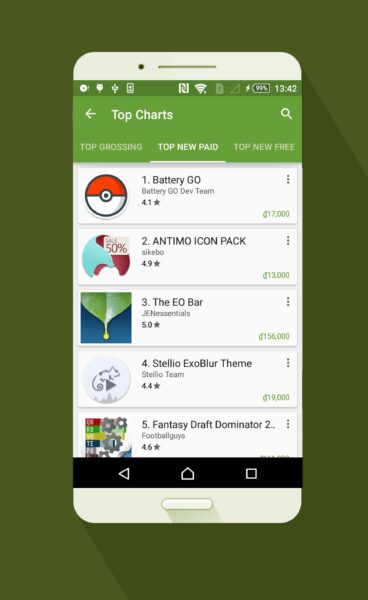
The official Android app store is tightly regulated. While there are ways to get around this, Google Bouncer is a dynamic heuristic malware detection program that protects Google Play, the official Android store. Employees at Google may also manually remove dangerous apps from the Play Store and remotely delete them from devices. Pirated and non-sophisticated malware is rapidly removed from the Google Play Store, while well-known and recognizable malware is never accepted.
Rooting
Some users “root” their phones, which means they make their phone’s root account constantly accessible. End users and end-user software do not generally have root access. Some modifications, installed software, and frequently flashing alternate operating system images to a device necessitate rooting.

The program is commonly installed on embedded devices to enable root access to apps. This program can also be utilized by malware, which eliminates the requirement for malware to run privilege escalation attacks on its own to gain root access.
PC-to-Device and Device-to-PC Infections
Infections from PCs to Android smartphones and vice versa are theoretically viable, as demonstrated by our prior work and demonstrated in practice by our proof-of-concept malware and recent malware. Vulnerabilities in operating system components, such as USB drivers or the file explorer, can be used to divert traffic from Android smartphones to PCs.
Post-Distribution Techniques
After the malware is placed on a target system, it uses a variety of ways to reach its final mode of operation. These methods are dependent on how the malware was first disseminated to a device and what the infection’s basic functioning is. Malware, in general, tries to gain the rights it needs to accomplish its goal.
edited and proofread by nikita sharma




